Restez informé de toutes les actualités et événements concernant PIM et DAM!
Web Accessibility: Why Alt Texts Matter
Web accessibility is now mandatory in Germany. Learn everything you need to know about it.
Read More
PIM Vendors: Comparing 7 Leading Systems
How do I find the right PIM vendor for me? What criteria should I consider? Learn more here.
Read More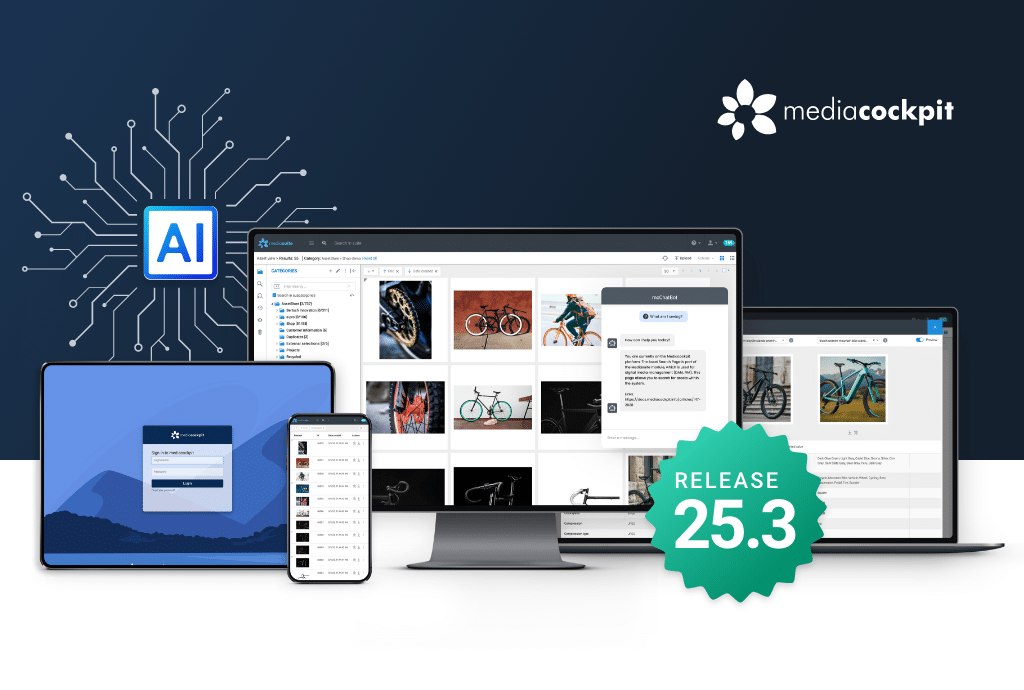
mediacockpit 25.3 Release
Cette version apporte de nombreuses améliorations sous le signe de l'IA - pour rendre la gestion des données produits & médias encore plus efficace.
Read More
Open Source vs. Proprietary PIM: Key Differences, Advantages, and Drawbacks
Understand the differences between open source and proprietary software & the pros and cons.
Read More
ePaper: Product Content Management with PIM & DAM
Good product content management is complex. However, it is very manageable with PIM and DAM software. Find out more in our whitepaper!
Read More
What is Master Data Management (MDM)? Definition and Meaning
Learn all about Master Data Management (MDM), its importance and how it can help your company.
Read More
Why Your Company Likely Needs PIM Software—And How to Win Your Boss Over
How a PIM helps data-driven companies massively + arguments on how to convince your boss.
Read More
Bertsch Innovation: Top PIM Vendor 2024
Top PIM Vendor 2024 - Bertsch Innovation sets standards in the PIM market with mediacockpit & AutomotivePIM.
Read MoreHighlighted Whitepaper
ePaper: Strategic Product Content Management with PIM & DAM
Comment optimiser la gestion du contenu produit pour un succès à long terme : Découvrez comment rationaliser vos flux de travail avec PIM et DAM. Notre livre blanc offre des informations pratiques et des stratégies éprouvées pour vous aider à mettre en place une approche évolutive, efficace et pérenne de la gestion du contenu produit.
Accomplir plus ensemble
Nous croyons en la valeur de la collaboration et de l’échange. Cela s’applique aussi bien à nos projets clients, desquels nous tirons de nombreuses informations précieuses pour le développement de nos produits, et à notre réseau de partenaires en pleine expansion, avec lequel nous soutenons nos clients dans leur numérisation.